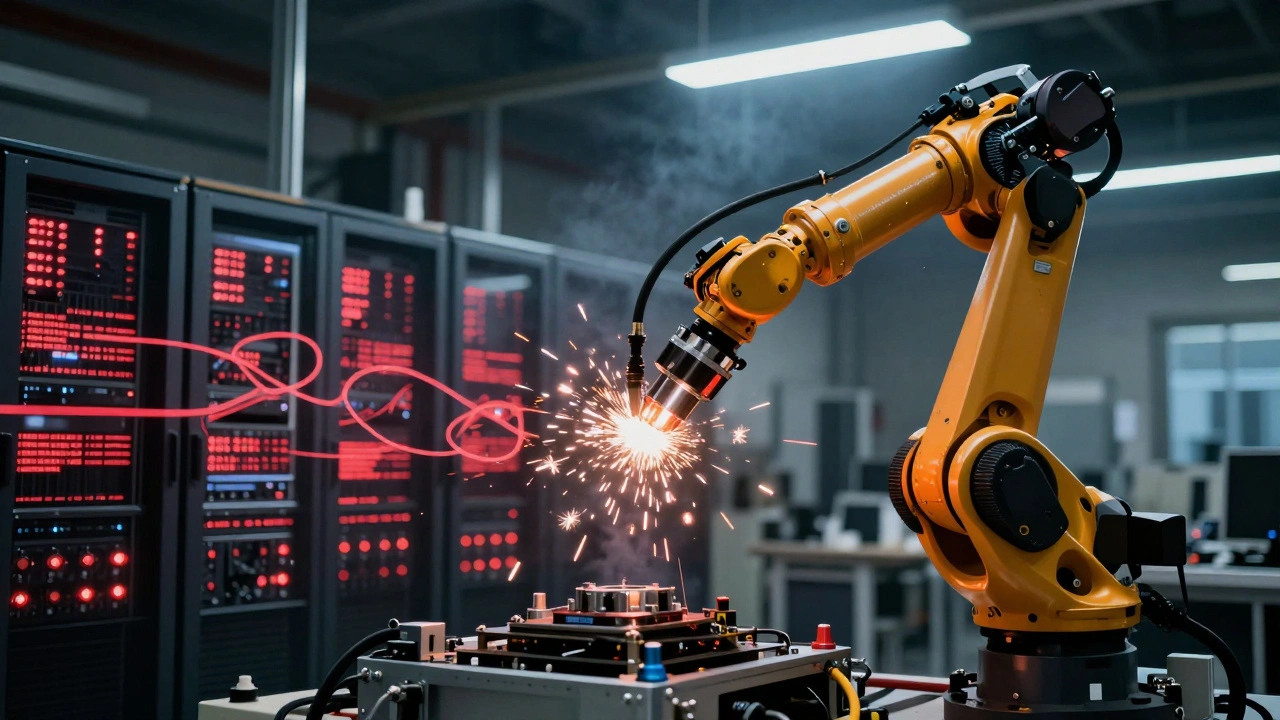
Industrial IoT Security is the comprehensive protection of interconnected industrial devices, networks, and data systems within manufacturing facilities and operational technology environments. Unlike traditional IT security, IIoT security addresses risks where cyber threats can cause physical damage to machinery or endanger workers. In 2025, a ransomware attack on a German automotive plant halted production for 72 hours, costing over $2.3 million. This isn't just a data breach-it's a real-world disaster.
When industrial systems connect to the internet, they become vulnerable to attacks that can physically damage equipment or disrupt critical processes. The convergence of IT (information technology) and OT (operational technology) means security must protect both data and physical infrastructure. As Jaycon Systems' 2026 guide explains, "industrial IoT controls physical processes. Mistakes cause real-world harm."
Why Industrial IoT Security Isn't Just IT Security
Traditional IT security focuses on protecting data and systems from unauthorized access. But in smart factories, security failures can literally break machines or stop production lines. This difference changes everything.
Consider a factory using Modbus or PROFINET protocols to control assembly robots. If hackers compromise these systems, they could force machines to overheat or malfunction. IT security tools often can't handle these legacy industrial protocols, which is why specialized OT security solutions are essential. Claroty's 2026 analysis states unequivocally: "Protecting IIoT devices within an OT environment demands a specialized, holistic approach. IT-centric tools aren't up to the challenge because they lack the specific protection that OT environments demand."
Another key difference is device constraints. Many industrial machines lack the processing power to run security agents. This means agentless security approaches-where protection happens without installing software on the device itself-are critical for legacy systems. Device Authority notes that "agentless methods provide security for devices you can't touch," making them indispensable for factories with older machinery.
Essential Security Requirements for Smart Factories
Robust IIoT security requires multiple layers of defense. Let's break down what works:
- Secure Boot ensures devices only run trusted firmware. Without it, attackers can install malicious code that survives reboots.
- Signed Firmware Updates with cryptographic verification (SHA-256 or stronger) prevent unauthorized code injection.
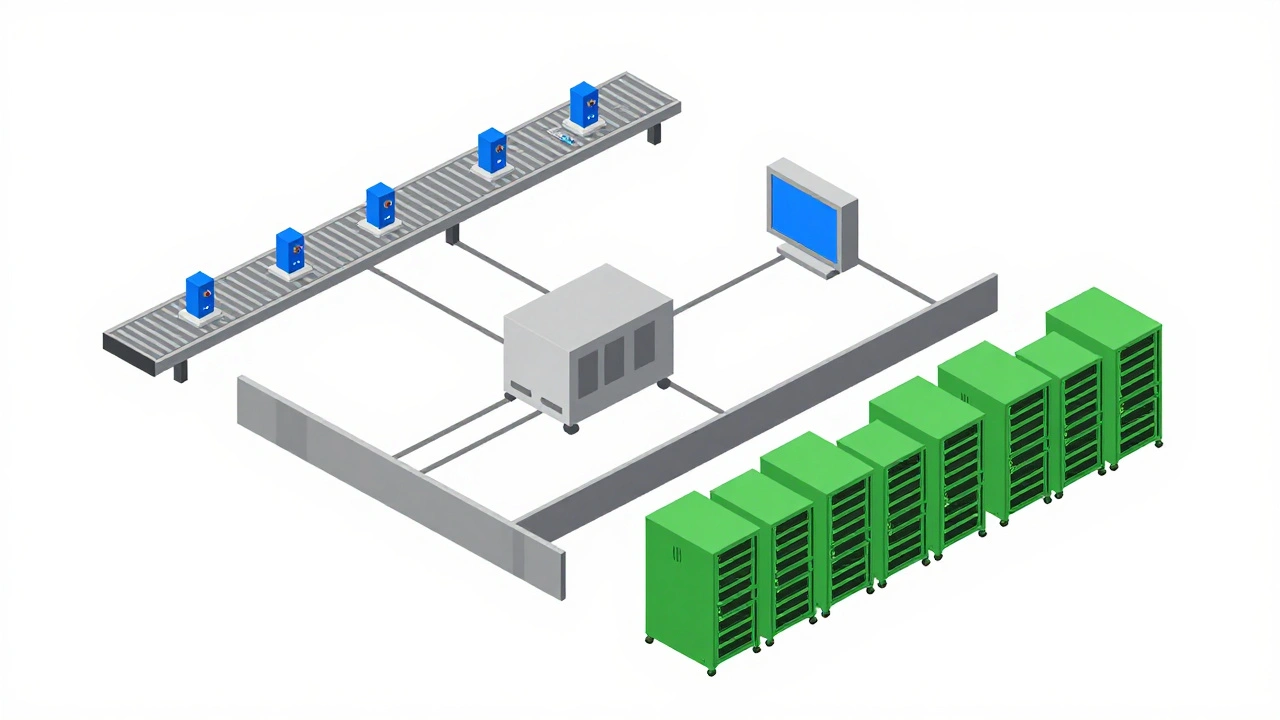
- Network Segmentation isolates IoT devices on separate networks, preventing small mistakes from becoming major incidents. Flat networks are especially dangerous.
- AES-256 Encryption for data at rest and TLS 1.3 for data in transit protect sensitive information.
Digi TrustFence® implements these standards through secure boot validation, hardened hardware, and network authentication. Bosch plant manager Elena Rodriguez confirmed in a 2025 case study that it reduced vulnerability detection time from 72 hours to 15 minutes while maintaining 99.999% uptime.
Compliance Mandates Driving IIoT Security
Regulations are pushing factories to adopt stronger security. The EU's NIS2 Directive requires compliance by October 17, 2026, mandating specific controls for secure access and encryption in IoT environments. Fabrity notes this is "an urgent matter" for manufacturers in 27 EU member states.
Similarly, IEC 62443 provides a comprehensive framework for industrial security. This four-part standard covers everything from general principles to product development requirements. Unlike general IT standards, IEC 62443 specifically addresses the unique risks of operational technology environments.
UL 2900-1 Certification tests IoT products for software vulnerabilities and encryption strength. UL's 2025 report found pass rates below 45% in initial certification attempts, showing how tough these standards are. Dr. Sarah Johnson of ISA emphasizes, "The best way to handle security issues related to IT/OT convergence is to improve monitoring via automation," noting manual processes can't keep up with 17,000+ unique industrial threat signatures identified in 2025.
Top IIoT Security Mistakes and Fixes
Many factories fail at basic security practices. Ponemon Institute's Q4 2025 report found 67% of facilities use default or weak credentials on at least 15% of their industrial devices. Reddit discussions in r/OTsecurity (January 15, 2026) show multiple engineers detailing ransomware infections from skipped firmware updates, costing $2.3 million per incident on average.
Here's how to fix these:
- No default credentials: Every device needs unique credentials. Shared secrets are a major vulnerability.
- Regular firmware updates: Siemens cybersecurity lead Markus Weber argues for staged updates with 30-day testing to prevent disruptions, but prompt patching is still critical. Balance is key.
- Network segmentation: Isolate IoT devices from core systems. A single compromised device shouldn't take down the entire factory.
Implementing proper network segmentation can be challenging-SANS Institute's December 2025 survey found 58% of organizations needed 6-9 months of engineering effort. But the alternative-like the 2025 German auto plant attack-is far worse.
OT-Specific vs. Traditional IT Security Tools
Not all security tools work for industrial environments. Here's how they compare:
| Feature | Traditional IT Security Tools | OT-Specific Security Solutions |
|---|---|---|
| Legacy Protocol Support | Limited or none | Modbus, PROFINET, OPC UA |
| Agent-Based Security | Requires software agents | Agentless options for resource-limited devices |
| Physical Safety Integration | Not designed for physical risks | Focus on preventing equipment damage |
| Compliance Standards | General IT standards | IEC 62443 and NIS2 compliance |
Market data shows OT-specific solutions are gaining traction. Gartner reports Claroty Platform has 38% market share among Fortune 500 manufacturers, while traditional IT security suites only achieve 12% adoption in industrial settings. IDC data shows pure-play OT security solutions grew 37% year-over-year in 2025, far outpacing IT security solutions targeting OT at 8.4% growth.

Practical Steps to Secure Your Smart Factory
Implementing IIoT security isn't a one-time project-it's a lifecycle process. Jaycon Systems recommends:
- Manufacturing phase: Unique provisioning, no shared secrets, controlled key handling
- Deployment: Harden configurations before devices go live
- Maintenance: Monitor vulnerabilities continuously and apply updates promptly
- Decommissioning: Remove trust, erase data, document removal
Training is critical. SANS Institute's 2025 OT Security Training Report states plant engineers need 120-160 hours of specialized training to manage IIoT systems effectively. Documentation quality varies significantly-IEC 62443-compliant solutions score 4.2/5 for clarity versus 2.8/5 for general IT tools adapted for OT use.
Community support is growing too. The ISA Global Cybersecurity Alliance and OT-specific subreddits have over 45,000 professionals as of January 2026. These forums provide real-world advice and troubleshooting help.
What's Next for Industrial IoT Security?
As we head into 2026, several trends are reshaping IIoT security:
- Edge AI: Mobotix reports 68% of new IIoT security implementations process threat detection at the edge, reducing latency from 500ms to under 50ms.
- Zero-Trust Architecture: ENISA's compliance report found 83% of EU manufacturers implemented strict verification protocols by Q4 2025, as required by NIS2.
- AI-Powered Monitoring: MIT's Industrial AI Lab 2025 study shows AI tools detect anomalies with 98.7% accuracy, though false positives remain a concern.
Forrester's Q1 2026 predictions suggest market consolidation, with 3-4 dominant players emerging by 2028. Organizations using comprehensive security based on IEC 62443 standards reduce breach likelihood by 89% compared to those using generic IT security approaches.
Frequently Asked Questions
What is the biggest mistake in IIoT security?
Using default or weak credentials. Ponemon Institute's 2025 report found 67% of manufacturing facilities have default credentials on at least 15% of their devices. This is often the first step attackers take to compromise systems. Always change default credentials and use unique, strong passwords for every device.
How does the NIS2 Directive affect manufacturers?
The NIS2 Directive requires EU member states to implement specific security controls for IoT environments by October 17, 2026. This includes encryption, secure authentication, and network segmentation. Non-compliance can result in fines up to 10 million euros or 2% of global turnover. Manufacturers outside the EU should also prepare, as many global supply chains require NIS2 compliance for EU customers.
Why can't I use regular IT security tools for my factory?
Traditional IT security tools often don't support legacy industrial protocols like Modbus or PROFINET. They also typically require software agents that older industrial devices can't run. OT-specific solutions like Claroty Platform or Digi TrustFence are designed to handle these challenges, providing protection without disrupting production. As Claroty states, "IT-centric tools aren't up to the challenge because they lack the specific protection that OT environments demand."
What is the role of network segmentation in IIoT security?
Network segmentation isolates IoT devices from core systems, preventing a single compromised device from taking down the entire factory. Jaycon Systems explains that "flat networks turn small mistakes into major incidents." Proper segmentation ensures that even if attackers breach one device, they can't move laterally to critical systems. This is why it's a foundational element of IIoT security.
How do I update firmware on industrial devices safely?
Firmware updates must be signed with cryptographic verification (SHA-256 or stronger) to prevent malicious code injection. Siemens cybersecurity lead Markus Weber recommends staged updates with 30-day testing periods to avoid operational disruptions. Always test updates in a controlled environment before deploying them to live systems. Digi TrustFence automates this process with secure boot validation and verified updates.