When your company gets hit by ransomware, it’s not the attack that breaks you-it’s the lack of a plan to bounce back. Most businesses think cybersecurity is about firewalls and antivirus software. But real resilience? That’s about knowing exactly how you’ll recover, who you can trust, and what happens when your vendor gets compromised. A cyber resilience roadmap isn’t a document you file away. It’s the living plan that keeps your business running when everything else is on fire.
Zero Trust Isn’t a Tool-It’s a Mindset
Zero Trust sounds like a buzzword, but it’s not about buying new software. It’s about assuming every user, device, and connection is already compromised. You don’t trust anyone until they prove they should be there. That means no more ‘inside the network = safe.’ Even your CFO’s laptop on the corporate Wi-Fi gets checked every time it asks for access to payroll data.
Real Zero Trust works in layers. First, verify identity with multi-factor authentication that changes with each login. Second, limit access. If someone only needs to view sales reports, they shouldn’t be able to download them or send them out. Third, monitor everything. If an employee logs in at 3 a.m. from a country they’ve never visited, the system should pause and ask for confirmation-not just block it.
Companies that get this right see breaches drop by 60% or more within two years. Why? Because attackers can’t move laterally. They hit one door, get stopped, and can’t find the next one. The key isn’t complexity-it’s consistency. Every application, every API, every cloud service gets the same strict rules. No exceptions.
Recovery Objectives: Know Your Numbers Before the Attack
After a cyberattack, time is money. But most companies don’t know how much money they can afford to lose-or how long they can go without systems. That’s where Recovery Time Objective (RTO) and Recovery Point Objective (RPO) come in.
RTO is how long you can stay down before customers leave, revenue vanishes, or regulators step in. For a hospital, RTO might be 15 minutes. For a small e-commerce store? Maybe 4 hours. For a manufacturing plant? 24 hours could mean missing a production cycle and losing a major client.
RPO is how much data you can afford to lose. If your finance system goes down, can you live without transactions from the last 10 minutes? Or do you need every single dollar recorded from the last 24 hours? Your backup schedule needs to match this. Backing up once a day won’t cut it if your RPO is 15 minutes.
Here’s what works: map out your critical systems. List them. Then assign RTO and RPO values to each. Don’t guess. Talk to your finance team, your customer service leads, your operations managers. They know what breaks first. Then build your backup and recovery plan around those numbers-not around what’s easiest to automate.
Third-Party Risk: The Hidden Weak Link
Over 60% of breaches in 2025 started with a vendor, not an internal mistake. Your IT team might be locked down tight, but if your cloud hosting provider, your payroll processor, or your marketing agency gets hacked, you’re next.
Most companies only check vendors for compliance certificates-ISO 27001, SOC 2, that sort of thing. But compliance doesn’t mean security. A vendor can have all the right papers and still use weak passwords, outdated software, or no encryption.
What actually works? Ask for proof of continuous monitoring. Not just annual audits. Ask: Do they scan for vulnerabilities daily? Do they patch within 72 hours of a critical alert? Do they have a breach response plan you can read? If they say ‘we follow industry standards,’ push back. Standards change. What’s standard today might be outdated tomorrow.
Start a vendor risk scorecard. Rate each one on: access to your data, frequency of security updates, incident response time, and whether they’ve had a breach in the last two years. Don’t just collect this data-use it. If a vendor scores below your threshold, you either fix it or find a new one. No exceptions.
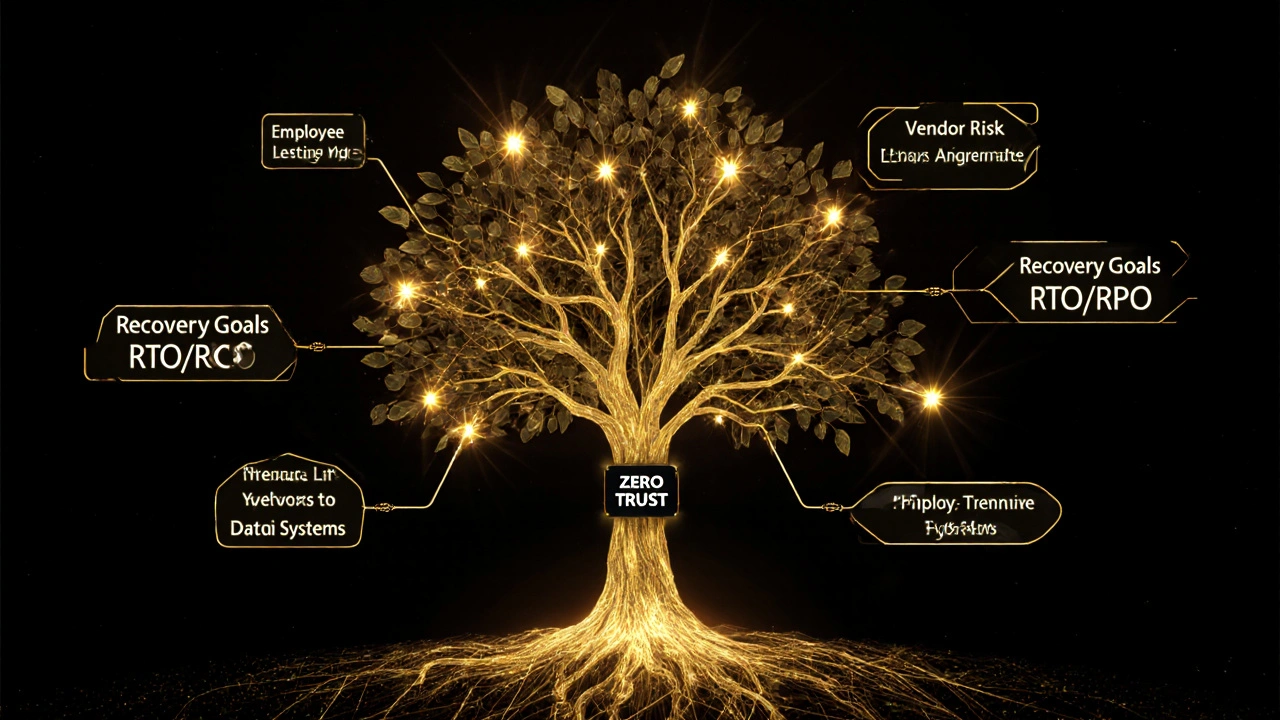
Putting It All Together: The Living Roadmap
A cyber resilience roadmap isn’t a PowerPoint deck you show to the board once a year. It’s a living document that gets updated every quarter. Start with three pillars: Zero Trust controls, recovery targets, and vendor risk ratings.
Each quarter, ask: Did we reduce access rights for non-essential staff? Did we test our backup restore process? Did we re-evaluate our top five vendors? If the answer is no to any of those, you’re falling behind.
Include real metrics. Not ‘we improved security.’ But ‘we reduced failed login attempts by 72% after enforcing device authentication.’ Or ‘we cut RTO for our CRM from 4 hours to 45 minutes by switching to real-time replication.’ Numbers tell the story. Stories get budgets approved.
And don’t forget the human side. Train your staff-not with a 30-minute video they skip, but with simulations. Run a fake ransomware attack. See how long it takes them to report it. See who panics. See who knows what to do. Make it real. Make it personal. People remember what they feel.
Common Mistakes That Break Resilience
Most roadmaps fail because they’re built on assumptions. Here are the top three mistakes:
- Assuming cloud = secure: Just because you use AWS or Azure doesn’t mean your data is protected. Misconfigured buckets and unpatched APIs are the #1 cause of cloud breaches.
- Ignoring legacy systems: That old inventory system from 2010? It might still run your warehouse. But if it can’t be patched, it’s a backdoor. Isolate it. Monitor it. Plan to replace it.
- Waiting for an incident to plan: If you’re writing your recovery plan after the breach, you’re already too late. Resilience is built before the fire starts.
Another trap? Thinking IT owns cyber resilience. It doesn’t. Finance owns RTO. Operations owns RPO. Legal owns vendor contracts. Everyone has a piece. The roadmap only works if leadership owns it-and holds people accountable.

Where to Start Today
You don’t need a $500,000 budget to begin. Start small, but start now.
- Identify your top three critical systems. What happens if they go dark for 2 hours?
- Ask your IT team: Are all users required to use MFA? Are any systems still on default passwords?
- Review your top five vendors. Do you have a written security agreement with each? Have you asked for their last penetration test report?
- Run a 1-hour tabletop exercise. Pretend your email system is down. Who calls who? What’s the backup plan? Write it down.
Do those four things in the next 30 days. You’ll know more about your resilience than 80% of companies.
What Comes Next
Cyber resilience isn’t a destination. It’s a rhythm. Quarterly reviews. Monthly checks. Real-time monitoring. Continuous training. The goal isn’t to be unhackable-it’s to be unbreakable. When the next attack comes, you won’t be scrambling. You’ll be executing.
Companies that do this right don’t just survive cyberattacks. They win. Customers trust them more. Investors see them as stable. Employees feel safer. And in a world where every business is a target, that’s not just good practice-it’s the only way to stay in business.
What’s the difference between cyber resilience and cybersecurity?
Cybersecurity is about preventing attacks-firewalls, encryption, access controls. Cyber resilience is about surviving them. It includes prevention, but also detection, response, and recovery. You can have strong cybersecurity and still collapse under a major breach if you don’t have a plan to bounce back. Resilience means you keep operating, even when things break.
Can small businesses afford a cyber resilience roadmap?
Yes-and they need it more than large companies. Small businesses are targeted more often because they’re seen as easier targets. You don’t need expensive tools. Start with free or low-cost options: enable multi-factor authentication everywhere, back up data daily using cloud tools like Backblaze or Google Drive, and ask your vendors about their security practices. The biggest cost isn’t money-it’s time. Spend 2 hours a month reviewing your plan. That’s enough to stay ahead of most threats.
How often should we update our cyber resilience roadmap?
At least every quarter. But you should review it after any major change: new software, new vendor, merger, acquisition, or after a near-miss incident. Technology and threats change fast. A roadmap that worked last year might be useless now. Treat it like your business plan-something that evolves with your company.
What if our vendors refuse to share security details?
Then you need to decide: is this vendor essential? If they handle your customer data, payroll, or critical operations, and they won’t tell you how they protect it, you’re taking a huge risk. You can’t control their security, but you can control your exposure. Limit what data you share with them. Use encrypted channels. Require them to sign a contract that holds them liable for breaches caused by their negligence. If they still refuse, start looking for alternatives. No vendor is worth your company’s survival.
Is Zero Trust too complicated for non-tech teams?
Not if you explain it in business terms. Zero Trust isn’t about tech jargon-it’s about protecting your money, your customers, and your reputation. You don’t need to understand encryption keys. You just need to know: if someone tries to access customer data without permission, the system should stop them-even if they’re on the inside. That’s not hard. And when your sales team knows their client data is safe, they’ll trust the company more. It’s a cultural shift, not a technical one.
Next Steps for Leaders
Start by gathering your key leaders: IT, finance, operations, legal, and customer service. Sit them down. Ask: If our main system went down tomorrow, what would break first? How long can we last? Who do we rely on outside the company? Write down their answers. Then build your roadmap from there.
Don’t wait for a breach. Don’t wait for a regulator to knock. The companies that survive are the ones that planned before the storm. Your roadmap isn’t just a plan-it’s your insurance policy. And right now, you’re underinsured.






